There is no day where you don’t hear about data breaches. Breaches where reputable companies are leaking out your personal information. You panicked last time you lost your phone, only to find it nearby, and promised yourself to take better care of your possessions.
Your devices are still laying around, your online presence is messy with gazillions of active and unused accounts. And now the Internet of Things, home appliances connected to the Internet, threatens your privacy more than ever. We say we don’t have anything to hide. This is true for many, but have you thought about the consequences if some stranger where to access your phone?
This article propose simple and efficient countermeasures you should consider to protect yourself against cyber threats. We trust that you will find these guidelines useful regardless of your level of technical expertise.
Backup Up Your Data

Your data is your digital life and consists of memories, documents, receipts, contracts, resumes and more. Like most, you probably have your photos stored “somewhere” and hope to revisit them when you get older. But why put yourself in the risk of loosing those irreplaceable memories? Even if your files are a mess they still deserve backups. All you need is to make a simple backup strategy once and for all.
Your first step to protect yourself against yourself and cyber attacks is to backup your data, and store it in a safe place. If your devices gets stolen or breaks, or you become victim of ransomware, you can recover your data instantly.
Choose a Backup Strategy
Storing your backup on external hard drives and storing them in different locations offsite is safest and fastest. This strategy give you full control of your data and you won’t need to worry about the ownership or bandwidth expenses. You still need to encrypt your data and there are many options available. VeraCrypt, an improved version of TrueCrypt, is free, easy to use and open source, and support full disk encryption enabling you to encrypt the entire drive. However, you won’t be able to access your data from elsewhere if choosing this strategy.
A more popular strategy is to use cloud storage. Cloud storage does not need to cost anything at all. If you are a student or employee, your university or employer may have included an Office 365 subscription with your account. You could already have 1000 GB of online storage at your disposal.
With most cloud services, you install an app to connect all your devices to the cloud. And your devices will synchronize and give you access to all your data from anywhere. To avoid being a single point of failure, your files will automatically spread across multiple data centers around the world.
The Risks When Using Cloud Storage
Although cloud providers aim to do their best to secure your data once stored in their public cloud environment, there is no guarantee that your data will not be part of a data breach. Therefore, organize your data based on its sensitivity and ask yourself if you are comfortable of having that data stored somewhere on the Internet, or if offline backups of your data is a better alternative.
Most cloud storage providers including Google, OneDrive and DropBox offer free subscriptions for new users. And if you opt for any of these we recommend that you create a new account using a random email address. An address not associated with your current email or name (identity) leaving your full name unexposed in the event of a breach.
Albeit having an attractive pricing plan, as well as convenient apps supported by most devices, we don’t recommend using Dropbox for storing your most important data due to their leaky past.
Organizing Your User Accounts

Until a few years ago many had just a handful of accounts to memorize. Today, however, in addition to keeping record of your work and school accounts, many enjoy a wide variety of free and subscription-based services from Netflix, Spotify and other online services. Thus, it is tempting to reuse credentials for convenience, and hackers are well aware of it. However, issues occur when one of your accounts exposes the credentials you use for accessing other services, leaving behind an open door for hackers to traverse their way through your digital life.
Use More Than One Email Address
Your email is the heart of your digital life since most services require an email address to signup for the services. Therefore, your email can recover access to your online services including Amazon, Facebook, Snapchat and Instagram. We tend to include our full name when choosing our email address. However, this in itself leave your vulnerable because it exposes your identity and hackers may use it to profile you. Historically majority of data breaches include database dumps with usernames and passwords. Therefore, the benefit of using this strategy is that when leaks occur it won’t expose your identity. Therefore, we recommend that you use three email accounts to manage your online presence.
The first email account is to be used for personal use such as when communicating with your employer, doctor, family or any individual likely to send you personal email. Because Gmail and Outlook are so popular and used by millions of users worldwide, these services are constantly being attacked. And therefore, your best option is to buy your own domain. Not only does a personal domain look more professional but it also keep you in control of your email.
The second account is to be used when signing up for partly trusted online services. Typically, this include hotel reservations, flights and other service where your email is stored in a central database accessible from the Internet.
The third account is to be used when signing up for untrusted services that carry a high risk of being attacked and that will likely leak your data at some point. These services include Spotify, Netflix, Facebook, Instagram, Job seeker websites and newsletters.
Use Password Managers to Protect Your Credentials and Speed Up Logins
Make sure that you use random passwords for all accounts so that if one account is compromised, the password cannot be used to access your other accounts. Finally, enable two-way authentication on your most important services so that a password alone can’t be used to logon to the services.
Password Managers such as KeyPass and PasswordSafe are free and popular standalone tools that you can use to manage your accounts and speed up logins. These tools give you a list of all your accounts thus reminding you to housekeep your online presence and delete unused profiles and accounts.
Many choose to use online services such as Dashlane, 1Password and LastPass for convenience. Be cautious about password managers accessible from the Internet as they are vulnerable to attacks. For this reason we do not recommended that you trust online password managers. Moreover, you don’t know the people behind these services or the infrastructure they run on. Why would you give away your passwords to someone else in the first place? Better off using your creativity such as hiding your passwords in a photo.
Protecting Your Devices
Your devices are the weakest link in your security chain. This is because they are the easiest target for hackers. You only need to lose your device, install malicious software or open emails with malicious attachments or links to infect them.
Enable Encryption to Prevent Data Theft
Encryption is the process of converting your data stored in your devices’ memory, from a readable format understood by humans and computers to a random format understood by neither. Only those who apply the correct key may decrypt, that is to unlock, the data.
Encryption does slow down your device a bit since additional compute power is necessary to encrypt and decrypt your data. However, it is worth it since breaking encryption is difficult and time consuming. Hence, in case of theft, thieves are likely to give up and erase your and reuse your devices.
If you own an Apple or Android device you can easily enable encryption under System Settings. If you run Windows then you can use BitLocker, a full disk encryption software developed by Microsoft. In addition, many products including laptops and workstations from companies such as Lenovo includes encryption software which enable you to protect your device.
Screen Passwords to Prevent Unauthorized Use of Your Devices
Your devices should be safe from unauthorized use. At a minimum you should use a screen lock to prevent others from using your devices. Ensure that you enable screen lock and set a password or pattern. Alternatively, use your biometrics such as face or finger to unlock your device.
Children or teenagers playing games or using social media while using your devices introduces new security risks. If you are in this situation, it is recommended, although not that convenient, to uninstall online banking and other sensitive apps from your device.
Update Your Devices
Make sure that your operating systems, apps, and browsers including Firefox, Safari and Chrome and extensions in particular, are up to date. The operating system and applications are likely keeping themselves up to date and patched. However, reboots are necessary to apply patches and also being the last stage that many tend to postpone. Check your Settings to verify that your devices are up to date.
Prevent Others From Monitoring Your Browsing Activity
The web browser is the most popular app that we use. And lot of sensitive information is communicated in that square box on your screen throughout the day. Most websites use HTTPS so that the communication between websites you visit and your browser is encrypted and protected from prying eyes. However, most websites place ads and other tracking mechanisms to follow you around on the Internet, even after you have left the website.
AdBlocker Ultimate is an excellent free ad-blocker that filters all ads once enabled in your browser. The best feature included with AdBlocker Ultimate is that it blocks all advertisements on YouTube.
Privacy Badger, another browser extension, prevents websites from tracking and monitoring your online activity.
Virtual Private Network (VPNs)
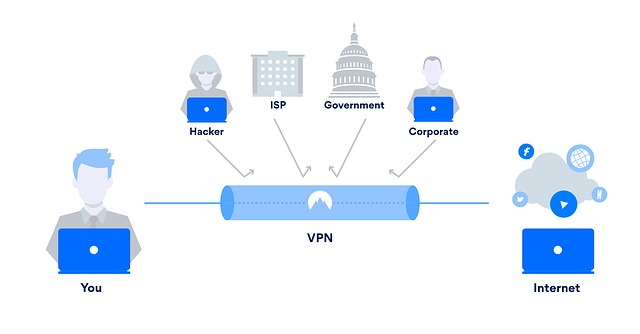
VPN, short for Virtual Private Network, is a technology that enable you to tunnel your communication via a third-party. VPNs enables telecommuting employees to access the organizations network and resources from home or when traveling. In the last two decades VPNs has become increasingly popular to use the technology to hide one’s internet presence.
VPNs are a safe and convenient countermeasure to protect yourself from cyber attacks. Especially when using public WiFi in airports and coffee shops where hackers may monitor your communication and steal your passwords. Once connected, you get to keep the same identity. Thus you are recognizable when using your online bank or Google account when traveling.
Typically, you install the VPN client once on your device and use your credentials to connect to your designated server. All your Internet activity will pass-through that server, hence your public identity will appear to be that of the server.
With the rise of VPN providers eager to offer you their low cost (or even “free”) VPN services you need to be very careful with whom you sign up with. These folks are hungry and waiting to monitor your Internet activity. We recommend using VPNs from reputable security firms such as F-Secure and not the most popular VPN providers such as NordVPN.
Delete Old Emails
Your inbox contains a wealth of information, from old conversations to online reservations and everything in between. The best way to avoid having your mailbox exposed is to delete those old emails that are occupying space. If you need to, you can always export your inbox or individual emails to a file and save it offline.
Wipe USB Devices
USB devices are a security risk because we always bring them with us or leave them behind in open spaces. Sometimes we also forget what we keep on them. Deleting a file or folder from your device only flags it as deleted and does not prevent someone from recovering it. Always store your USB devices in a safe place and ensure that you erase and format them after use. Preferably use VeraCrypt or other encryption software to protect your USB device.
Cover Your Camera
Your devices are equipped with cameras capable of exposing your identity. Cyber criminals are increasingly using cameras as part of their ransomware and sextortion attacks. Always cover your camera when not used. A piece of paper and some tape or a sticky note works well.
